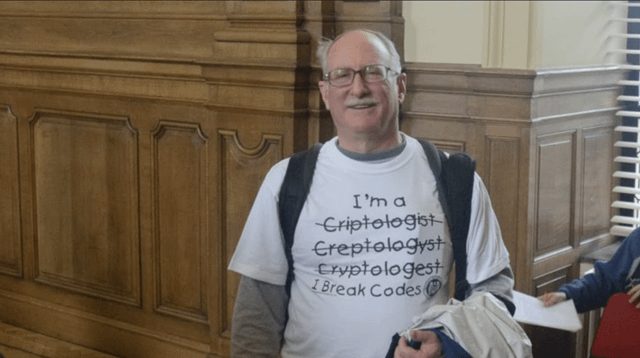
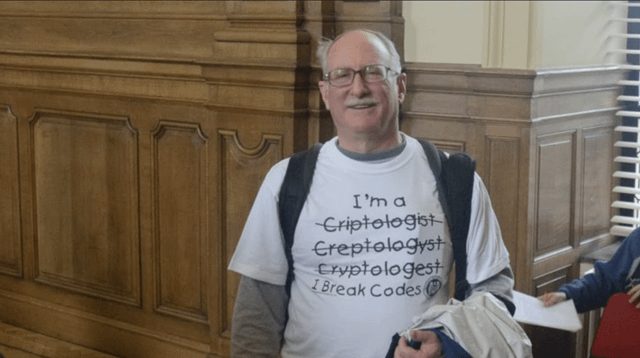
In a surprising admission, Bill Burr, the author of the controversial 2003 NIST password guidelines, has expressed regret over his recommendation for organizations to require password changes every 90 days. Burr now believes this policy has led to more harm than good, urging a reevaluation of how passwords are managed in today's digital landscape. This comprehensive guide covers bill burr man who wrote in detail.
Understanding the Original Guidelines
In 2003, the National Institute of Standards and Technology (NIST) published a set of guidelines aimed at strengthening password security across various sectors. Burr, who was working with NIST at the time, played a pivotal role in crafting these recommendations. The guidelines suggested that users change their passwords every three months, a directive intended to mitigate the risk of unauthorized access to sensitive data. Originally reported by r/Damnthatsinteresting.
Regarding bill burr man who wrote, Regarding bill burr is the man who wrote the 2003 nist manual that recommended password changes every 90 days. he now regrets creating that guideline because it just encourages people to make small alterations to weak passwords ("password1" to "password2")., However, Burr's approach was based on the prevailing belief that frequent changes would enhance security. This perspective was widely accepted across industries, leading many organizations to adopt the policy as a standard practice. Yet, this well-intentioned guideline inadvertently encouraged a culture of weak passwords. Instead of creating strong, memorable passwords, users often resorted to simple modifications, such as changing "password1" to "password2," which did little To Improve overall security.
Burr's Change of Heart
Fast forward to today, and Burr has publicly stated his remorse regarding the 90-day password change recommendation. In interviews, he has highlighted the unintended consequences of his guidelines, emphasizing how they failed to address the root issue of password security. "I wish I had never written that guideline," Burr admitted, acknowledging that the policy has led to a false sense of security among users.
Regarding bill burr man who wrote, Regarding bill burr is the man who wrote the 2003 nist manual that recommended password changes every 90 days. he now regrets creating that guideline because it just encourages people to make small alterations to weak passwords ("password1" to "password2")., Experts in cybersecurity have echoed Burr's sentiments, arguing that frequent password changes can actually lead to weaker passwords. The psychological toll of constantly changing passwords can cause users to choose easily guessable alternatives, making systems more vulnerable to breaches. The shift in perspective has sparked discussions among security professionals about the need for a more nuanced approach to password management that prioritizes user behavior over arbitrary timelines.
The Evolving Landscape of Password Security
As technology continues to advance, the conversation around password security has evolved significantly. The rise of multi-factor authentication (MFA) and biometric verification methods have provided alternatives to traditional password use, prompting many organizations to reconsider their password policies. MFA, for instance, requires users to provide two or more verification factors, making unauthorized access much more difficult.
Regarding bill burr man who wrote, Regarding bill burr is the man who wrote the 2003 nist manual that recommended password changes every 90 days. he now regrets creating that guideline because it just encourages people to make small alterations to weak passwords ("password1" to "password2")., Furthermore, NIST has updated its guidelines in recent years, moving away from rigid password expiration policies. The latest recommendations emphasize the importance of creating strong, unique passwords and suggest that organizations should only request password changes when there is evidence of a breach or compromise. This shift marks a significant departure from Burr's original guidelines, reflecting a deeper understanding of user behavior and security needs.
Lessons Learned and Moving Forward
Burr's admission serves as a crucial reminder of the importance of adaptability in cybersecurity practices. As threats evolve, so too must the strategies designed to combat them. Organizations are encouraged to prioritize user education, helping individuals understand the significance of strong passwords and the risks associated with using easily predictable combinations.
Regarding bill burr man who wrote, Regarding bill burr is the man who wrote the 2003 nist manual that recommended password changes every 90 days. he now regrets creating that guideline because it just encourages people to make small alterations to weak passwords ("password1" to "password2")., Moreover, the conversation surrounding password management underscores a broader trend in the tech industry-moving away from outdated practices and embracing innovative solutions. Cybersecurity experts advocate for password managers, which can generate and store complex passwords, alleviating the burden on users to remember multiple credentials.
Regarding bill burr man who wrote, Regarding bill burr is the man who wrote the 2003 nist manual that recommended password changes every 90 days. he now regrets creating that guideline because it just encourages people to make small alterations to weak passwords ("password1" to "password2")., In light of Burr's reflections, it's clear that while the original guidelines may have been well-intentioned, the key to robust cybersecurity lies not just in rules but in fostering a culture of security awareness and proactive measures. Organizations must remain vigilant and adaptable, reassessing their practices to ensure they are equipping users with the tools necessary to navigate an increasingly complex digital landscape.
Regarding bill burr man who wrote, Regarding bill burr is the man who wrote the 2003 nist manual that recommended password changes every 90 days. he now regrets creating that guideline because it just encourages people to make small alterations to weak passwords ("password1" to "password2")., As we look to the future, the challenge remains: how can organizations ensure their security measures effectively safeguard sensitive information without compromising user experience? Burr's insights may serve as a valuable starting point for this ongoing dialogue.